-
96 %
Reduction in
spam emails -
91.66 %
Decrease in
Recovery Time Objective -
375 %
Increase in
malware detection rate
Challenges & Opportunities
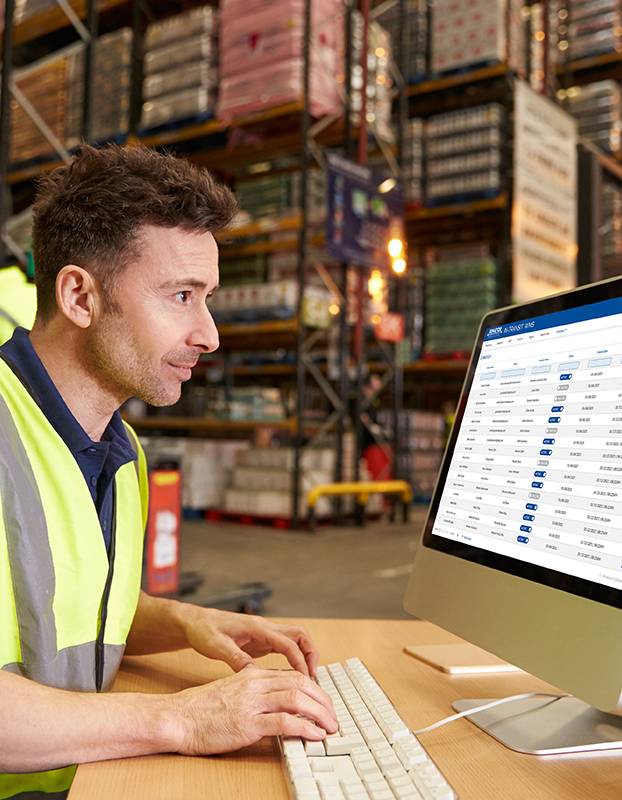
A manufacturer was experiencing system security exploits and continuous business downtimes that slowly affected its reputation and revenue-generating activities. The company contacted Cyzerg to explore the reasons that led to the challenges and recommend an effective security and data protection strategy.
Cyzerg discovered that the manufacturer received continuous email phishing attacks, resulting in hackers compromising users and company information. Additionally, critical business data was encrypted by ransomware, and the company was demanded to pay a ransom. Because of this incident, the business suffered disruptions, which led to revenue loss. Finally, the company lost credibility among its customers and partners due to the cybersecurity breach.
Solutions
After understanding the manufacturer's challenges, Cyzerg recommended implementing comprehensive security and data protection strategy.
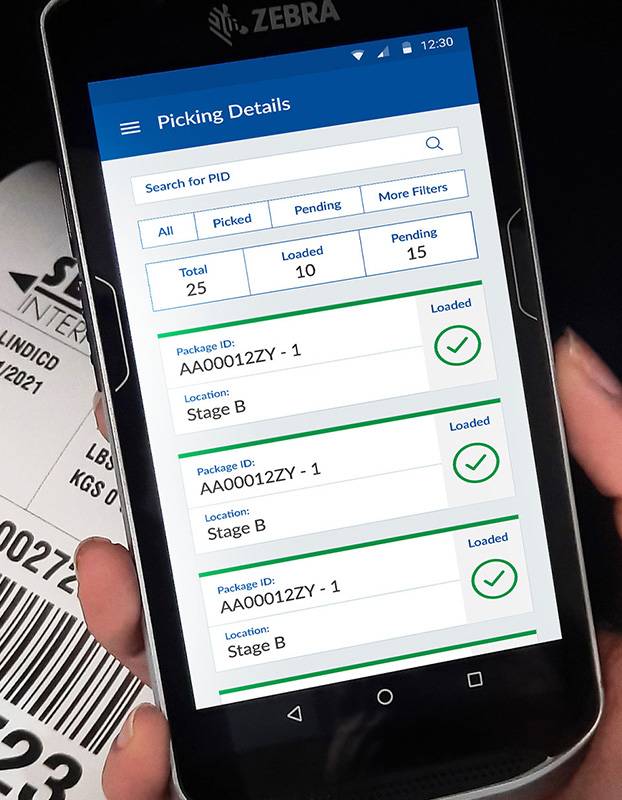
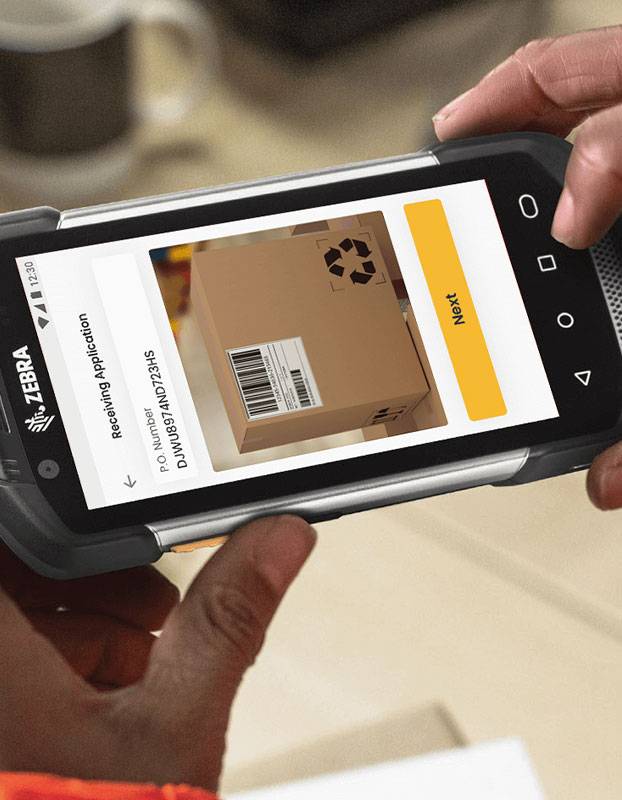
To execute the solution, Cyzerg implemented advanced email filtering capabilities and security policies, and conducted cybersecurity awareness training for end-users. Additionally, endpoint and threat detections solutions were deployed to detect and stop cybersecurity attacks. All endpoints across the organization were also hardened, and strong access controls were implemented. Finally, an advanced hybrid backup solution with cloud-based disaster recovery capabilities was deployed.
Results
Once Cyzerg's security and data protection strategy was implemented, the manufacturer reduced spam emails, ransomware, and phishing attacks from reaching end-users. Additionally, the company increased its detection rate of malware and reduced cybersecurity exposure. As a result, the client was able to increase accountability across all end-users and system administrators. Lastly, the manufacturer established reliable data protection mechanisms and reduced RTO and RPO times.
With the achieved results, the manufacturer reduced the system security exploits and continuous business downtimes it faced. The company was also able to re-establish its credibility among its customers and partners by keeping its systems and data secured.
Reduce Disruptions with Cyzerg's Data Security
Cyzerg will never sell, rent or otherwise distribute your information. Click here to read our full privacy policy.